27 Jan 2015: The Future of the Dark Net in Summary
Seeking anonymity in an Internet panopticon
‘Dear Sirs, I would like to buy some marijuana …’
In the second event of our new Hyperhabitat series of events, Cybersalon set out to explore the controversial role of Tor encryption and it’s impact on contemporary culture. We wanted to examine what recent events, such as FBI attempting to break Tor, mean for users of the trusted anonymous tools. Tor, known also as used by Laura Poitras to contact Edward Snowden prior to his NSA leak.
It is a sophisticated amalgam of anonymity software that protects users by routing traffic through encrypted connections. Like any encryption or privacy system, Tor is also popular with criminals.
Tor was hacked for the first time by the FBI as a part of so-called “Operation Torpedo” in 2012. The US Dept. of Justice is now holding a court hearing on the exploit, scheduled for February, with the legality of the attack questioned by encryption experts. With so many legitimate users depending upon the system, any successful attack on Tor raises alarm and prompts questions.
Not many people have explored and probed the fringes of Tor as deeply as Jamie Bartlett, Director of the Centre for the Analysis of Social Media at Demos and author of the newly published exposé The Dark Net. We invited him to share his cyber-voyage findings, in conversation with Wendy Grossman, computer and privacy journalist and author of Net.Wars book and Dr Gareth Owen, a cybersecurity and digital forensics researcher at University of Portsmouth who has reported on his recent headline grabbing Dark Net study.
Representing the encryption developers community was Bjarni Runar Einarsson, co-author of encrypted email Mailpile, Jon Baines, digital anonymity activist and Rich Metson, co-author of Off Grid (a surveillance simulation game).
They joined to discuss the pros and cons of such heavily encrypted networks, issues of human rights and Tor’s future use in, as Bryan Ford argues, our seeking anonymity in an internet panopticon.
The Dark Net- the voyage into the underworld
In his recently published Dark Net book Jamie Barlett takes a hands-one approach and plays Malinowski to the digital Dark Net Triobranders, using a form of participatory observation in his field-work of examining the Dark Net locals.
He dives right into the anonymous cyber High Street and buys marijuana on SilkRoad 2.0, finding it of satisfactory quality, also noting the widespread availability of Fairtrade cocaine (20% profits going to educational projects). He is pleasantly surprised at the high quality of the customer service and impeccable turn of phrase on their letters.
He observes Vex, a celeb of the subterranean world of live webcam sex shows and notes her motivations to be fairly comparable with average entrepreneurial Silicon Valley start-up enthusiast.
Not just a digital tourist, Jamie travels to Catalunia to spend time in Calfou bitcoin commune. Here, under the Spanish sun, in a small mountainous village, the hard-working programmer Amir Taaki is building his version of Dark Wallet for Bitcoins, the cryptocurrency that started on the Dark Net but now is moving mainstream. It is now accepted by Microsoft and many others, showing that the Dark Net is often a birth place of tech innovation that then spreads to wider society.
Jamie also notes that the Dark Net and suburbian shopping meet online, as the top spot on Tor’s bestsellers list were fake Tesco vouchers, worth 20 pounds. In his view, under the heavy veil of secrecy and encryption, Dark Net is fairly human after all. He does not give in to the atmosphere of ‘moral panic’, but he does note that ‘in the future, it will be easier to hide and harder to censor’ as more Net users learn to use the anonymity tools.
Much controversy accompanied the publication of The Dark Net. Ian Hargreaves, in his thorough review accused the author of a liberal attitude to the anonymised Tor, frowning at Jamie’s even-handed depiction of the Dark Net inhabitants as essentially a mirror of human society rather than a nest of vipers that the media would like it to be.
Others, like Wendy Grossman , recommend his cybervoyage to the underworld (link http://www.zdnet.com/article/the-dark-net-book-review-tales-from-the-internet-underworld/, noting the high quality and validity of his first-person account of the world not many of us experienced. We need to be open about those undercover societies, study them and educate the society about it’s true nature in order to make decisions about their future in a rational, not fearful manner.
When Malinowski (whom Jamie resembles not just with his unkempt hair and charismatic voice) worked on Sexuality of the Triobranders, he broke many taboos of the day and introduced understanding of non-Western cultures to the puritan and repressed Europeans of the beginning of the XX century.
By exploring the Dark Net with an open mind, Jamie Bartlett has hopefully kicked off a healthy trend where discussion of what people want to do in the anonymity of their digital journeys is going to be conducted with technical historical knowledge as well as an ethical perspective, instead of scaremongering, hiding behind taboos and moral panics that we so often see as a typical media reaction to anyone mentioning the mysterious Dark Net.
‘What you can measure you can manage’ goes the old saying and his book is bringing some hope to driving the debate into the realm of rationality and away from Daily Mail sales-chasing hysterical headlines.
Media Bias and the Dark Net – here comes Dr Own
These media panics and propensity to ‘bad news bias’ were hard at play in response to Dr Gareth Owen’s recent study of Tor and the extent of illegal pornography available on it’s servers.
He explained his methodology of counting the average number of accesses to the illegal, or ‘hidden’ Tor content (which as he acknowledged himself accounts for only 2% percent of the overall traffic). He has noted that although the number of servers with hidden content were small, a high number of the visits were to the child abuse sites.
The manner of counting the visits was questioned by a number of respected encryption researchers as those numbers were considered likely to have been generated by bots, security researchers and child abuse agencies that crawl the Internet for illegal sites continuously .
However, true to form, the media, including those who should know better (BBC and The Guardian among others) took advantage of the topic being of a complex nature, and went with headlines that ‘80% of Tor traffic is child abuse sites’.
The study is impossible to verify as the average illegal site gets taken down from Tor very quickly and over the 6 months of Dr Owen’s study, a large majority of the sites would have been indeed taken down, making replicability unlikely. Jamie Bartlett notes that Internet Watch Foundation has confirmed, it takes them only 1 hour from notification of the existence of the site, to the action of taking it down.
To clarify, Dr Owen has also confirmed that it is possible to take the sites down with or without permission of the Tor developers, so there is a degree of control over what sites are functioning on Tor networks. He notes that ‘as a tool for preventing censorship, it is surprisingly easy to censor Tor users and content via consensus distributed blocklists’, implementing blocklists in a transparent way being easier with consent of the Tor dev team.
If the study has flaws or is inconclusive, we need to debate them in more detail as the impact on a flaky study on legislation can be significant in the atmosphere of moral panic in the media. Wendy Grossman notes the infamous Cyberporn study from 1995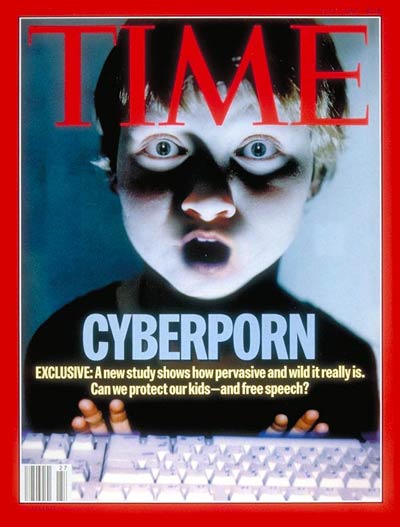 which led to implementation of censorship legislation, only to be disproved shortly after due to failings in the methodology of the non-peer-reviewed study. The media were to blame as The Time magazine ran the study on it’s front cover, lending credibility to what was essentially undergrad quality work. The debate about the risks of Tor and it’s adventages will continue as more studies need to be conducted to improve our understanding of the nature of the anonymous online traffic, risks and benefits to be debated in an open dialogue with all the stakeholders.
which led to implementation of censorship legislation, only to be disproved shortly after due to failings in the methodology of the non-peer-reviewed study. The media were to blame as The Time magazine ran the study on it’s front cover, lending credibility to what was essentially undergrad quality work. The debate about the risks of Tor and it’s adventages will continue as more studies need to be conducted to improve our understanding of the nature of the anonymous online traffic, risks and benefits to be debated in an open dialogue with all the stakeholders.
Take charge of your personal privacy online
“50 shades of Gray” was the title of a document shared with the participants and audience of the Dark Net debate, listing the key tools that we all can use to protect personal privacy online. Ben Greenway and Jon Baines presented their selection of the anonymity tool du jour, to open the options to people who simply want to claw back the ownership of their own data.
The government’s attempts to bring increased surveillance without a debate has led to loss of trust by the Internet users and an increased impetus to protect our digital privacy by encryption of communications. Following the earlier increase in government’s surveillance powers introduced in July despite objections from experts and users alike, the post-Snowden distrust of government intentions is just another step alienating the digital community.
Mailpile is one of the new generation of encrypted solid email tools nearing it’s launch, and Bjarni, it’s co-author is focusing on improving the User Experience in the drive to make it accessible to general public.
It affords the choice for the individual and Cybersalon have pledged to join the beta test to remind ourselves what life used to be like before Google made a mockery of a concept of a ‘private letter’, before Facebook decided that they ‘own’ every letter you post to your close friends, before the state and corporate giants usurped the ownership of our digital breadcrumbs.
When we encrypt our communication in the UK or US, we are presumed criminal, which is wrong. This needs to be addressed via technology in the current situation when the government is not prepared to enter an educated dialogue about the rules of engagement of surveillance with the UK users.
However, Jamie Bartlett observes that if Mailpile and its ilk is successful, it will increase the costs of surveillance for plethora intelligence agencies and more wider intelligence will be needed in the absence of access to email. The balance of privacy and security needs to be debated in the context of price, as ultimately we are the taxpayers that have to find the budgets for GCHQ working harder if encrypted email becomes the norm.
In fact Bjarni puts the price of cracking the encrypted emails at £10,000 per person, so quite an increase from the current £0.12 per person that the intelligence agencies spend today per email..
Stalled progress on Surveillance oversight in UK
Delegating the decision about surveillance oversight to RUSI has been questioned as the main commercial sponsor of Royal United Services Institute is Palantir, world’s largest supplier of surveillance software to UK and US, turning about $1bln in fees. Clearly they not neutral, and are not going to be voting for less surveillance. Palantir management has questionable ethics, with Joe Landsale currently named in a sexual assault lawsuit and their presence on the RUSI board is questionable to say the least.
Considering the above, the oversight process of national surveillance should be addressed again and fast, with all the stakeholders declaring their commercial interest before being invited to assess the ethics of blanket surveillance. Alternative is to more anonymity tools putting the price of surveillance up, but since we fund it from taxes, that is clearly a least preferred scenario.
How does it feel to be under constant surveillance?
Off Grid, the game designed by Richard Metson is one of the new tools emerging that allow the full experience of surveillance state following to it’s logical conclusion.
Rich is an Open Communications activist and has been grappling with the problem that only a few people who have experienced Stasi East Germany or Communist Poland shared the oppressive and destructive nature of those systems (best example is Timothy Garton Ash, UK journalist, whose personal view from the times when he was under surveillance by the Ministry for State Security has been published recently.
Meeting like-minded people at http://gamesforchange.org/festival/, Richard has realised that in order to visualise the surveillance-by-state experience, he needs to create the world when the hero is faced with increasing loss of privacy and has to learn new ways to avoid being reduced to an object in a perfect panopticon.
Since the Snowden revelations, he included more real-world examples like the scene where the protagonist has to destroy his laptop in the basement in order to satisfy the requirements of the State Surveillance The Guardian. The system in the game is powered by an AI engine that taps into PRISM-like omnipresent environment, where the decisions about your future are being made by algorithms, and there is no recourse from their judgment. That Kafkasque reality is very similar to what Tim Garton Ash describes in this analysis of his personal Stasi file experience. It also amply demonstrates that the game simulating surveillance experience is the best way to educate people about the impact of blanket digital spying on society under surveillance.
Gathering versus “looking” at data – is there a difference?
Some in the surveillance circles are promoting the notion that ‘gathering’ of information on people is different than ‘looking at it’ or ‘surveillance’ as noted by Geoff While, Channel 4 Tech News Editor and author of Secret Life of Your Mobile Phone. Off Grid game dispels this and shows the gray implications of the separation of permission to ‘gather’ verus ‘look at the data’.
Once gathered, your data will stay there, somewhere on a data farm, retained longer and longer by intel agencies in the hope for improved decoding technology where the encryption can be broken. As Chris Baraniuk notes in Wired, the data ‘gathered’ but not ‘looked at’ will stay in the data centres for ever, passed from regime to regime regardless who wins the next elections, or finds themselves in power. This is not a risk a democratic society should be taking without a wide and thorough educated debate.
While data sits in datacentres, it can be used by the wrong people for the wrong reasons or just be at risk of security leaks as has happened so often before.
The Dark Net audience argued that the automation of surveillance does not make it different than being spied on by human observers. The 180 km of Stasi files may look out of date now  , as the intelligence agencies store and process petabytes of information today, but the psychology of ‘perceived’ feeling of being under digital surveillance is the same as being observed by your neighbours in Stasi East Germany, if you are aware of it at all.
, as the intelligence agencies store and process petabytes of information today, but the psychology of ‘perceived’ feeling of being under digital surveillance is the same as being observed by your neighbours in Stasi East Germany, if you are aware of it at all.
Self-censoring in the age of blanket surveillance
In discussions following the talks, the majority of the the researchers and security journalists in the audience report self-censoring (most of hands went up when asked if they self-censor when online or writing on surveillance and Tor) and not covering the stories they should. The perception of being under surveillance and awareness of risks for the researchers is increasing and the clarity of the research rules and scope of investigations is declining.
This confirms recent Pew Institute findings that Americans self-censor online more than in physical settings since Snowden’s announcements.
As our researchers are under risk, and continue to self-sensor out of fear of persecution, the knowledge about the Dark Net and extremism will shrink, limiting the understanding of the real rather than media-induced risks for us in the UK and elsewhere. Wendy Grossman noted that David Brin’s thoughts on Transparent Society need to be revived. Today, his stipulation that the surveillance should be symmetrical with at least the stakeholders who are selected by the society to oversee the surveillance process brings another option to broaden the new thinking on the dialogue with the government.
Today our privacy is asymmetrical, surveillance oversight is concentrated in less than trusted (or competent) hands and the educated minority that understands what is happening to us on the Internet, is self-censoring for the fear of being criminalised.
As long as that holds true, Tor and anonymous privacy tools will be supported by community Kickstarters to improve mainstream encryption.
The debate will continue at our third event on the HyperHabitat, focusing on new technology impact on Smart City program and on resilience in urban surveillance in the era of Internet of Things.
Suggested reading:
- Jamie Bartlett, The Dark Net
- Bryan Ford, Seeking Anonymity in an Internet Panopticon
- Wendy Grossman, The Dark Net: Tales from the internet underworld
- Wendy Grossman, Hadrian’s Firewall: UK’s New Internet Filter or Censor?
- Wendy Grossman, Pelican Crossing
- Wired, Laura Poitras on the crypto tools that made her Snowden film possible
- Wired, FBI used Web’s favourite hacking tool to unmask Tor users
- Electronic Frontier Foundation, Surveillance Self Defence
- Electronic Frontier Foundation, 7 privacy tools that were essential to making CitizenFour.
- BBC, Tor study suggests most visited Hidden Services sites host child abuse images.
- Wired, Over 80% of Dark Web visits relate to paedophilia, study finds.
- SC, Tor creators debate validity of dark web traffic study findings.
- Motherboard, Police busted a Darknet bot
Videos to watch:
Dr Gareth Owen reports his latest study findings on Dark Net Tor Hidden Services usage